In today’s digital-first world, web applications are the backbone of how businesses interact with their customers. With increasing user data being handled online, ensuring robust security is no longer optional—it is a fundamental requirement. At MaxValid, we focus on building scalable and secure applications, and one of the core aspects of that is authentication. Authentication ensures that only legitimate users can access the application and its resources, protecting both user data and business logic.
Traditionally, applications relied on session-based authentication, where the server maintained the state of each user. While this approach works, it doesn’t scale well for modern applications, especially those built as microservices or deployed in cloud environments. Here is where JSON Web Tokens (JWT) come into play. JWT enables stateless authentication, making it easier to manage and secure APIs while allowing applications to scale seamlessly.
Why JWT Matters
JWT is a compact, URL-safe method for representing claims to be transferred between two parties. Essentially, it allows servers to issue secure tokens after a user successfully logs in or registers, which the client can then use to authenticate subsequent requests. These tokens are signed, ensuring their integrity and authenticity, and they often include an expiration time, which limits the window during which a token can be used.
By integrating JWT in Spring Boot applications, developers can:
- Eliminate the need for server-side session storage.
- Ensure stateless authentication that scales across distributed services.
- Provide secure and time-bound access to APIs.
- Make token generation and validation a centralized, reusable process.
At MaxValid, we leverage JWT as part of our standard authentication workflow to ensure that our applications remain both secure and performant.
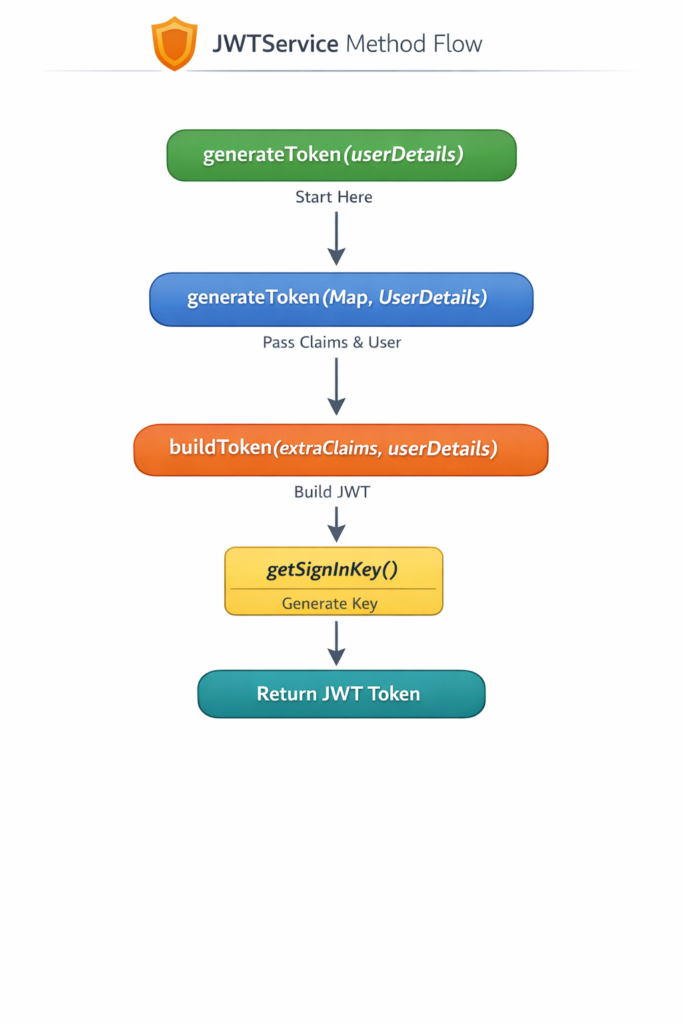
JWT Token Generation Workflow
The JWT token generation process typically occurs during two main scenarios:
- User Registration: When a new user signs up for your application.
- User Login: When an existing user authenticates with valid credentials.
Both workflows eventually lead to the creation of a JWT token, which is issued to the client. Let’s dive into how this works in Spring Boot using our JwtService.
Step 1: generateToken(UserDetails)
The generateToken method is the starting point. It takes a UserDetails object—Spring Security’s standard way of representing authenticated users—and orchestrates the token creation. This method defines the claims, such as:
- Subject: Usually the username or email of the user.
- Issued At: The time when the token is generated.
- Expiration: When the token will expire.
- Roles or Authorities: To define user permissions.
Once these claims are defined, generateToken calls the buildToken method to create a signed JWT.
Step 2: buildToken()
The buildToken method is responsible for constructing the JWT using a signing algorithm and secret key. In Spring Boot, the most common approach is using HMAC SHA256. The token consists of three parts:
- Header: Specifies the algorithm and token type.
- Payload: Contains claims such as username, roles, and expiration time.
- Signature: Ensures the token hasn’t been tampered with.
By building the token in a dedicated method, we ensure that token creation is centralized and reusable across both login and registration workflows.
Step 3: getSignInKey()
A critical step in token security is signing. The getSignInKey method generates a secure signing key, often using a base64-encoded secret. This ensures that tokens are cryptographically secure and cannot be easily forged. At MaxValid, we emphasize the importance of using strong, random secrets and rotating them periodically.
How Token Generation Integrates With Registration
During user registration, the workflow is as follows:
- The client sends a registration request with user details.
- The application validates the input and creates a new user in the database.
- Once the user is successfully created, the
JwtService.generateTokenmethod is invoked. - A JWT token is generated and returned to the client as part of the registration response.
This approach provides an immediate, secure authentication mechanism for new users without requiring a separate login step. It also ensures that the application remains stateless, as the server does not store any session data.
How Token Generation Integrates With Login
Similarly, during login:
- The client sends credentials (username/email and password).
- The application authenticates the user using Spring Security.
- Upon successful authentication,
JwtService.generateTokenis called. - The generated JWT token is returned to the client.
The client can then include this token in the Authorization header for subsequent API requests. The server will verify the token for each request, ensuring that only authenticated users can access protected endpoints.
Key Advantages of JWT Generation in Spring Boot
Implementing JWT generation in a Spring Boot application brings multiple benefits:
- Statelessness: No need to maintain sessions in the server. This reduces memory usage and simplifies deployment across multiple instances.
- Security: Each token is signed and time-bound. Unauthorized modification invalidates the token.
- Scalability: Stateless tokens allow easy scaling of services, including microservices, cloud deployments, and serverless applications.
- Centralization: By using a dedicated
JwtService, token creation logic is centralized, making it easy to maintain, update, and audit. - Flexibility: JWT can carry additional claims like roles, permissions, or custom metadata to enforce fine-grained access control.
Best Practices for JWT Token Generation
At MaxValid, we follow industry best practices to ensure robust JWT security:
- Use strong signing algorithms: Prefer HMAC SHA256 or RSA keys over weaker algorithms.
- Set proper expiration times: Avoid long-lived tokens. Use refresh tokens if longer sessions are required.
- Secure storage of secrets: Never hardcode signing keys. Use environment variables or secure vaults.
- Monitor token usage: Log token generation events and monitor for anomalies.
- Rotate keys periodically: Rotate signing keys to reduce the impact of potential leaks.
@Value("${jwt.secret}")
private String secretKey;
@Value("${jwt.expiration}")
private long jwtExpiration;
private Key getSignInKey(){
byte[] keyBytes = Decoders.BASE64URL.decode(secretKey);
return Keys.hmacShaKeyFor(keyBytes);
};
private String buildToken(Map<String, Object> extraClaims, UserDetails userDetails, long jwtExpiration){
return Jwts.builder()
.setClaims(extraClaims)
.setSubject(userDetails.getUsername())
.setIssuedAt(new Date(System.currentTimeMillis()))
.setExpiration(new Date(System.currentTimeMillis() + jwtExpiration))
.signWith(getSignInKey(), SignatureAlgorithm.HS256)
.compact();
};
public String generateToken(Map<String , Object> extraClaims, UserDetails userDetails){
return buildToken(extraClaims, userDetails, jwtExpiration);
}
public String generateToken(UserDetails userDetails){
return generateToken(new HashMap<>(), userDetails);
};Real-World Implications
For modern applications, JWT is not just a technical choice—it is a business-critical decision. A secure authentication flow:
- Protects sensitive user information.
- Reduces risk of data breaches.
- Provides a foundation for building scalable microservices.
- Enhances customer trust and confidence in your application.
At MaxValid, we integrate JWT as part of our standard authentication workflow for every application, ensuring our clients’ systems are secure, scalable, and ready for growth.
Conclusion
JWT token generation is a central piece of modern web application security. By using Spring Boot and a dedicated JwtService, developers can ensure that both user registration and login are secure, efficient, and stateless. Every token issued is time-bound, cryptographically signed, and ready to authorize API requests, enabling safe and seamless interaction across services.
By following best practices, centralizing token creation, and using secure signing mechanisms, applications can meet today’s high standards of web security while remaining scalable and maintainable. At MaxValid, our approach to JWT generation ensures that our clients benefit from secure authentication without compromising user experience or performance.
#SpringBoot #JWT #JavaSecurity #WebSecurity #Authentication #TokenBasedAuth #Microservices #MaxValid