Spring Boot JWT Authentication – Final Dependency Order (Developer Guide)
When implementing JWT-based authentication in Spring Boot, one common source of confusion is understanding the correct dependency order.
Questions like:
Which class should be created first?
Which component depends on which?
If the dependency order is not respected, developers often face issues such as:
Bean not found errors
Circular dependency problems
AuthenticationManager not working
JWT filter not triggering properly
Below is a proven, dependency-based creation order that works smoothly in real-world Spring Boot applications.
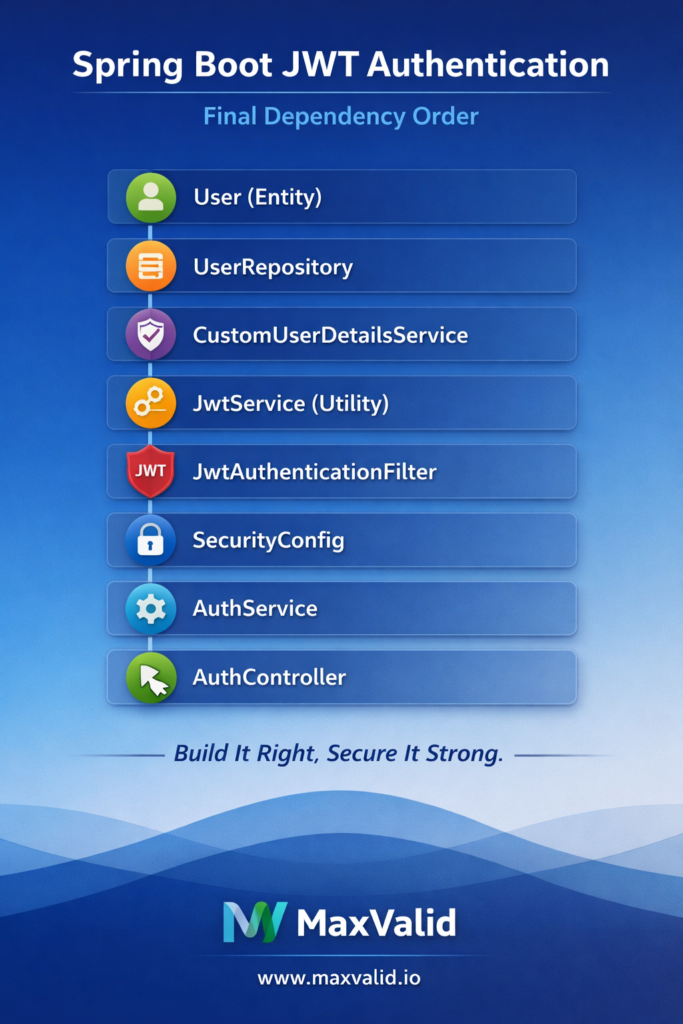
JWT Authentication – Final Dependency Order
User (Entity)
UserRepository
CustomUserDetailsService
JwtService (utility for token generation and validation)
JwtAuthenticationFilter
SecurityConfig
AuthService
AuthController
Why this order matters
UserDetailsService is mandatory.
Without it, the AuthenticationManager cannot authenticate users.
JwtAuthenticationFilter depends on JwtService and UserDetailsService.
The filter must validate tokens and load user details before setting the security context.
SecurityConfig depends on the JWT filter and AuthenticationManager.
This is where the security chain is assembled.
Controllers should always be last.
Controllers do not define security rules; they only consume the secured flow.
Golden rules to remember
If a class is injected into others, it should be created first.
If a class implements an interface, the implementation must exist before usage.
Controllers always come last.
Benefits of following this order
Cleaner and more predictable architecture
No circular dependency issues
Easier debugging
Production-ready JWT security flow
At MaxValid, we design authentication systems by following clear dependency boundaries to ensure scalable, secure, and maintainable Spring Boot applications.
#MaxValid #maxvalidio #SpringBoot #SpringSecurity #JWT #Authentication #Authorization #BackendDevelopment #Java #APISecurity #CleanArchitecture #SoftwareEngineering