In modern web applications, issuing a JWT token is only half the story. Once a token is generated and provided to a client, every subsequent API request must be carefully validated to ensure that it comes from a legitimate user and that the token hasn’t been tampered with. Token validation is a critical part of maintaining application security, integrity, and trust, and it forms the backbone of stateless authentication workflows in Spring Boot applications.
At MaxValid, we prioritize both token generation and token validation to ensure that our applications remain secure, reliable, and scalable.
Why JWT Token Validation Matters
JWT tokens are self-contained tokens that carry authentication and authorization information, including user identity and permissions. They are signed to prevent tampering. However, simply issuing a token is not enough:
- Tokens can expire, and expired tokens should no longer grant access.
- Tokens could be maliciously modified if not verified correctly.
- Tokens may contain claims that need to be interpreted safely to control access to resources.
Without robust validation, an application could be vulnerable to unauthorized access, leading to data breaches or misuse of sensitive features.
Validation ensures that each incoming request is legitimate, the token is current, and the user has the appropriate permissions for the requested resource.
The JWT Validation Workflow in Spring Boot
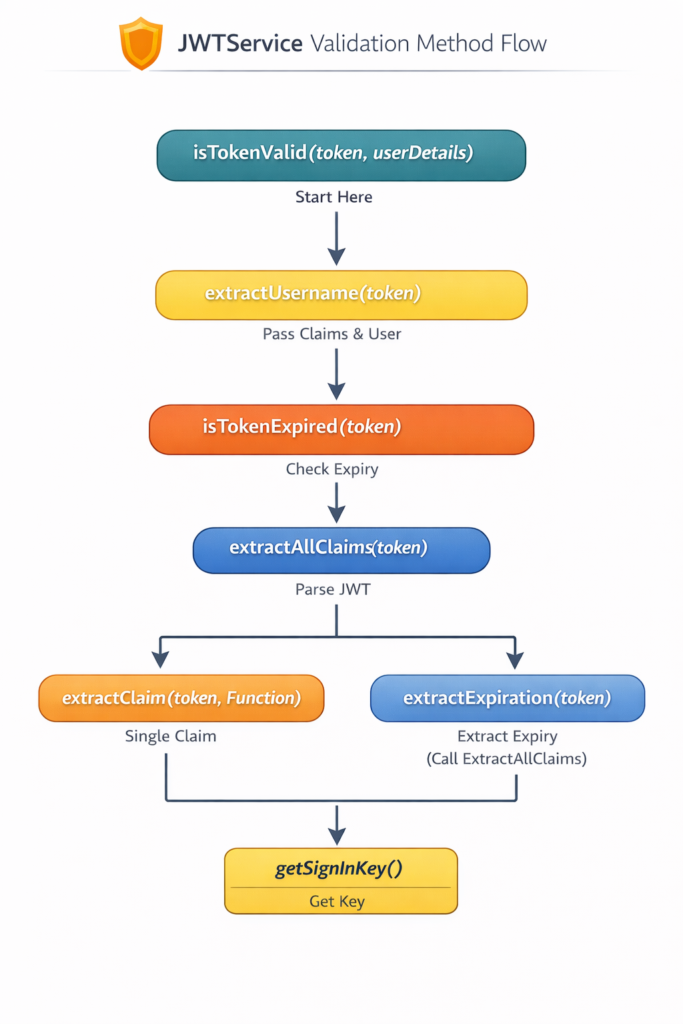
In Spring Boot applications, the JwtService or a dedicated utility class often handles token validation. Let’s break down how this workflow typically works and why it is essential.
1. isTokenValid()
The isTokenValid method is the primary entry point for token validation. It performs multiple checks, including:
- Comparing the username stored in the token with the username of the authenticated user.
- Checking the expiration date to ensure the token is still valid.
- Optionally verifying user roles or permissions if required.
This method ensures that only valid, unexpired tokens are considered for further processing.
2. extractUsername() and extractClaim()
JWT tokens store multiple claims, such as the subject (username), issued time, expiration, and custom metadata. To access these securely, the JwtService uses:
extractUsername()→ retrieves the username from the token claims.extractClaim()→ retrieves any specific claim safely, such as roles or user ID.
By isolating these methods, we ensure that claims are accessed safely, reducing the risk of misinterpretation or accidental exposure of sensitive information.
3. extractAllClaims()
At the heart of token validation is parsing the JWT payload. The extractAllClaims() method decodes the token and reads its content. This includes standard claims such as sub (subject), iat (issued at), exp (expiration), and any custom claims included during token generation. Parsing all claims allows the application to:
- Verify token integrity.
- Inspect claims to enforce role-based access control.
- Ensure consistency between the token and the application’s expectations.
4. getSignInKey()
One of the most critical steps in JWT validation is verifying the signature. The getSignInKey() method retrieves the secret key used to sign the token. When the token is verified against this key:
- Any modification of the token invalidates it.
- The application can trust that the token originated from a legitimate source.
- It prevents attackers from forging tokens or escalating privileges.
At MaxValid, we use strong, secure signing keys and rotate them periodically to maintain a high level of security.
@Value("${jwt.secret}")
private String secretKey;
@Value("${jwt.expiration}")
private long jwtExpiration;
private Key getSignInKey(){
byte[] keyBytes = Decoders.BASE64URL.decode(secretKey);
return Keys.hmacShaKeyFor(keyBytes);
};
public boolean isTokenValid(String token, UserDetails userDetails){
final String username = extractUsername(token);
return (username.equals(userDetails.getUsername())) && !isTokenExpired(token);
};
private Claims extractAllClaims(String token){
return Jwts.parserBuilder()
.setSigningKey(getSignInKey())
.build()
.parseClaimsJws(token)
.getBody();
};
public <T> T extractClaim(String token, Function<Claims, T> claimsResolver){
final Claims claims = extractAllClaims(token);
return claimsResolver.apply(claims);
};
public String extractUsername( String token){
return extractClaim(token, Claims::getSubject);
};
private Date extractExpiration(String token){
return extractClaim(token, Claims::getExpiration);
};
private boolean isTokenExpired(String token){
return extractExpiration(token).before(new Date());
};
How Token Validation Integrates With Spring Security
In a typical Spring Boot application:
- The client sends an API request with the JWT token in the
Authorizationheader. - A JWT filter intercepts the request before it reaches the controller.
- The filter calls
isTokenValid()in the JwtService. - If the token is valid, the filter sets the authentication context in Spring Security.
- If the token is invalid or expired, the filter rejects the request with an unauthorized response.
This approach keeps the application stateless because no session data is stored on the server. Each request is self-contained with the JWT token, making the system scalable and suitable for microservices or distributed environments.
Key Benefits of Separating Token Validation From Generation
It is important to note that token validation is a separate responsibility from token generation. While the JwtService handles both tasks, separating concerns has several advantages:
- Maintainability: Each method is focused on a single responsibility, making the code easier to test and maintain.
- Security: Validation logic can be enhanced independently to include new checks such as IP verification, token blacklisting, or additional claim inspections.
- Scalability: Stateless validation allows the same token validation logic to be applied across multiple services without central session storage.
- Resilience: Applications remain resilient to expired or tampered tokens, and malicious attempts are blocked efficiently.
At MaxValid, this separation of concerns ensures that our applications are robust, reliable, and secure, even as they scale.
Best Practices for JWT Token Validation
To maximize security, we follow best practices during validation:
- Always verify the token signature: Never trust the token without checking its cryptographic signature.
- Check expiration: Reject tokens that have expired. Use short-lived access tokens combined with refresh tokens for longer sessions.
- Validate claims: Ensure that roles, user IDs, or permissions match the expectations of your application.
- Handle errors gracefully: Invalid or expired tokens should return clear, secure error messages without exposing sensitive information.
- Centralize validation logic: Use a dedicated service like JwtService to avoid duplication and maintain consistency across your application.
Real-World Implications
Proper JWT validation directly impacts user trust and system security. Applications that fail to validate tokens are at risk of unauthorized access, data leaks, and potential compliance violations. Conversely, a robust validation workflow ensures that:
- Only authenticated users can access sensitive endpoints.
- The application remains stateless, lightweight, and scalable.
- Security practices align with modern standards for microservices and cloud-native systems.
By implementing a structured JWT validation workflow, businesses can scale confidently while maintaining the highest level of security.
Conclusion
JWT token validation is a critical step in modern web application security. While generating tokens ensures users can authenticate, validation ensures that only legitimate, unexpired tokens are honored. Using Spring Boot and a dedicated JwtService, developers can:
- Safely extract claims from tokens.
- Verify token signatures and expiration.
- Set the authentication context for secure API access.
- Maintain a stateless and scalable authentication workflow.
At MaxValid, we integrate JWT validation as a core part of our application security strategy, ensuring that all API requests are both authentic and authorized. By following best practices and separating validation from token generation, we provide applications that are secure, reliable, and ready to handle modern business demands.
#SpringBoot #JWT #TokenValidation #WebSecurity #JavaDev #MicroservicesSecurity #StatelessAuth #DevWorkflow #MaxValid